Application Layer of OSI Model
What is Application Layer of OSI Model
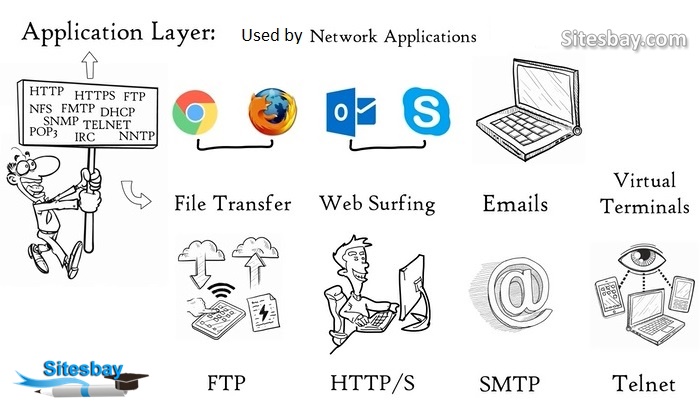
Application layer is the top most layer in OSI and TCP/IP layered model and it is used by the Network Application. Network Application means computer applications the use internet like google chrome, firefox, skype etc. Web browser is a network appliction running in your computer. Browser don't reside in the application layer but it uses application layer protocals like HTTP and HTTPs to do web surfing. The application layer is a layer in the Open Systems Interconnection (OSI) seven-layer model and in the TCP/IP protocol suite. It consists of protocols that focus on process-to-process communication across an IP network and provides a firm communication interface and end-user services.
It is the top most layer of OSI Model. Manipulation of data(information) in various ways is done in this layer which enables user or software to get access to the network. Some services provided by this layer includes: E-Mail, transferring files, distributing the results to user, directory services, network resources, etc.
The application layer provides full end-user access to a variety of shared network services for efficient OSI model data flow. This layer has many responsibilities, including error handling and recovery, data flow over a network and full network flow. It is also used to develop network-based applications.
More than 15 protocols are used in the application layer, including File Transfer Protocol, Telnet, Trivial File Transfer Protocol and Simple Network Management Protocol.
The application layer uses More than 15 protocols, including File Transfer Protocol, Telnet, Trivial File Transfer Protocol, and Simple Network Management Protocol, etc.
It provides interfaces and support for services such as electronic mail, remote file access, and transfer, shared database management, directory services, network resources, etc. and other types of distributed information services also.
Services Provide by Application Layer
- Simple Mail Transfer Protocol
- File transfer
- Web surfing
- Web chat
- Email clients
- Network data sharing
- Virtual terminals
- Various file and data operations
Design Issues with Application Layer
There are commonly reoccurring problems that occur in the design and implementation of Application Layer protocols and can be addressed by patterns from several different pattern languages.
- Pattern Language for Application-level Communication Protocols
- Service Design Patterns
- Patterns of Enterprise Application Architecture
- Pattern-Oriented Software Architecture
Services of Application Layers
Network Virtual terminal
The application layer is the software version of a physical terminal and this layer permitted to a user to log on to a remote host. For this, an application creates a software emulation of a terminal at the remote host. By this user's computer can communicate with the software terminal, which in turn, communicates with the host. It is shown that the remote host is communicating with one of its terminals, so it allows the user to log on.
File Transfer, Access, and Management (FTAM)
An application permits a user to access files in a remote computer, to retrieve files from a computer and to manage files on a remote computer. FTAM is concerned with a hierarchical virtual file in terms of file attributes, file structure and the types of operations performed on the files and their attributes.
Addressing
To achieve communication between client and server system, there is a need for addressing. When a request is sent from the client side to the server side, this request contains the server address and its own address. The server answered to the client request, this request contains the destination address, i.e., client address. DNS is used to achieve this type of addressing.
Mail Services
Email forwarding and storage of e-mails provided by an application layer.
Directory Services
A distributed database is contained by an application that provides access for global information about various objects and services.
Authentication
It provides authentication to occur between devices for an extra layer of security and it authenticates the sender or receiver's message or both.

